Is This Normal? - NSRL with Malware Analysis
About The Project
Continuing from my Malware Analysis Pipeline project, I have been spending some
time tearing apart samples trying to get better at malware analysis. Doing so,
I run across files that I’ve never heard of before. Obviously, Google is the
first stop during the triage period of an unknown function call/DLL, etc…
However, what if the DLL dropped was a modified version of a legitimate application?
This is where the NSRL comes into play.
National Software Reference Library (NSRL)
Beyond just google it!, The National Institute of Standards and Technology publishes a list of hashes (MD5/SHA-1) containing product names, file sizes, manufacturer identifiers, and other various product information. This list is known as the National Software Reference Library. While NIST does host a query service, you can also download the CSV file to slice and dice any way you’d like.
NSRL into Elasticsearch
After quickly parsing the CSV file and storing the data into Elasticsearch, the end-user can easily pair executables of interest with what exists within the NSRL.
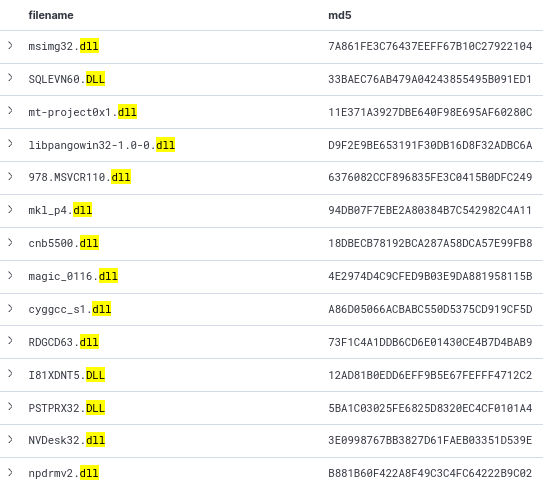
The image above shows an abbreviated query pairing the DLL file names to MD5 hashes.
Extending The Functionality
Integrating a simple HTTP client (assuming you’re using Elasticsearch as a backend) into existing RE tools as plugins would allow analysts to see if the hash of the DLL you currently have loaded into your tool of choice matches up with the NSRL list of “known good”. The same methodology is applied to a list of “known bad”.
Thank you for reading! Feel like I missed something? Tweet @me and let me know!